Sell Network Security As A Service To Reach More Customers
By The Business Solutions Network
As network security threats continue to grow and become more complex, cloud-based security solutions are playing a growing role in helping VARs and MSPs protect their customers.
When you look at some of the cloud-related headlines and hear about companies such as Amazon, Apple, and Microsoft having cloud outages and/or coming under attack from white hat hackers (i.e. those who hack a company’s cyber defenses for the altruistic purpose of helping the company solve its security problems) as well as their unethical counterparts, the cloud may seem like the last place where you’d want to move your customers’ security resources. However, when you look at research from the leading security research firms and network security experts, a different picture emerges.
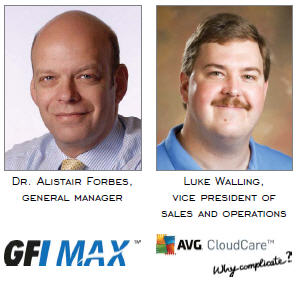
Over the past few years the SANS Institute, a securityfocused cooperative research and education organization that reaches more than 165,000 security professionals around the world, worked with a consortium of U.S. and international agencies to develop what’s known as the Critical Security Controls (CSC). This list of security controls focuses on prioritizing security functions that are effective against the latest advanced targeted threats, with an emphasis on providing best practices for defending against the threats. The U.S. State Department reported that, by following the top 20 controls outlined in the CSC, it was able to reduce its measured security risk by more than 94 percent. “The Defence Signals Directorate [DSD] in Australia estimates that 85 percent of targeted attacks could be mitigated by implementing the top 4 security controls in the SANS Top 20 list of CSC,” says Dr. Alistair Forbes, general manager at GFI MAX. Two of the four are patching operating systems and applications to ensure that vulnerabilities are eliminated. Implementation of AV (antivirus) software is a further security protection. “Both of these types of solutions require continuous updating — set it and forget it is not effective — and they are therefore both wellsuited to being sold as a monthly service,” says Forbes.
Another security practice where VARs and MSPs (managed services providers) should consider changing their business model is vulnerability scanning. “Periodic manual network scans are insufficient at identifying and alerting on potential vulnerabilities in a timely manner. This is another area where resellers should consider offering frequent, automated scans as a service to better protect their customers,” says Forbes.
Luke Walling, vice president of sales and operations at AVG, concurs with Forbes’ list of network security staples that are a fit to be sold as a service — via the cloud — and adds, “Any security software that manages and audits network usage is another good fit. For example, software that tracks DLP [data loss prevention], resource utilization, mobile devices joining the network, and/or gateway utilization would be a good fit to deploy in the cloud and sold as a monthly service.”
Potential Pitfalls To Selling Security As A Service
When it comes to making the necessary business changes to offer vulnerability scanning, application patching, and AV updates as a service, Forbes advises resellers to watch out for a couple of common pitfalls, including investing too much of your engineers’ time delivering a cloud-based solution and ensuring that switching to the as a service offering doesn’t open up your company to unnecessary liability. He suggests MSPs define a set of policies for the various types of devices that are being managed. Once defined, it should be possible to apply these policies automatically to all devices under management. “MSPs should also look for integrated reporting that allows them to see the status of all the systems they are managing and identify quickly any issues requiring attention,” he says. “Ideally, it should be possible to manage remediation actions from a centralized console without any need to access the machine(s) one at a time to manage any exceptions.”
Walling concurs and adds, “One of the biggest time drains for engineers is spent uninstalling legacy on-premises software to prepare for cloud-based software. Make sure your security vendor offers a rip-and-replace tool that allows engineers to use a software wizard to define the uninstall parameters once [e.g. remove all security applications] and automatically apply those business rules across the entire enterprise.”
With regard to liability, Forbes advises MSPs to document exactly what’s included and what’s not in their security service and to explain to customers how security incidents will be handled. “Setting clear expectations up front with the customer is key to avoiding any disagreements in the event of an incident, which is the time at which everyone will be most concerned about what has happened and why,” he says.
Overall, moving AV, patch management, or vulnerability scanning to the cloud presents minimal risk, according to Walling. “However, when you start moving personally identifiable data to the cloud, that’s where you need to pay attention to liability concerns,” he says. “This could include cloudbased solutions that track Internet surfing habits, monitor emails, and track backed-up data.” When sensitive data is involved, VARs and MSPs need to make sure they’re only working with vendor partners they can trust. The first thing is to make sure you’re working with a cloud provider that supports the highest level of data encryption (e.g. 256-bit key AES encryption) and has passed the audit requirements for the highest level of security standards, which is SSAE (Statement on Standards for Attestation Engagements) 16. “VARs and MSPs should also look closely at the reseller agreements their vendor partners and cloud providers ask them to sign,” says Walling. “Never sign anything until you know your IT provider’s contingency plan if they go out of business and/or if they suffer a data breach. Specifically, make sure they’re not planning to make something that’s their problem become your problem.”
Moving your network security offerings to the cloud can open new doors to recurring revenue for your practice while at the same time improving your ability to protect your customers. By doing your due diligence and heeding Forbes’ and Walling’s advice, you can shorten this transition process and minimize your risks.
